A Comprehensive Guide to Palo Alto Zone Based Firewall for Beginners
A Comprehensive Guide to Palo Alto Zone Based Firewall for Beginners
What is Palo Alto Networks Firewall?Palo Alto Networks offers a selection of firewall technologies made to safeguard networks and data from online dangers. An internal network and the internet are separated by a network security device called the Palo Alto Networks firewall. Based on a set of specified security policies, it analyses incoming and outgoing communication and blocks any suspicious or malicious activity.
For complete protection for businesses of all sizes, Palo Alto Networks firewalls employ a next-generation security strategy that integrates network security, cloud security, and endpoint security.
The intrusion prevention, antivirus, and anti-spyware functions of the firewalls may all be combined into a single platform thanks to a unique operating system called PAN-OS. This gives a uniform view of the organization's security posture and lessens the complexity of administering several security solutions.
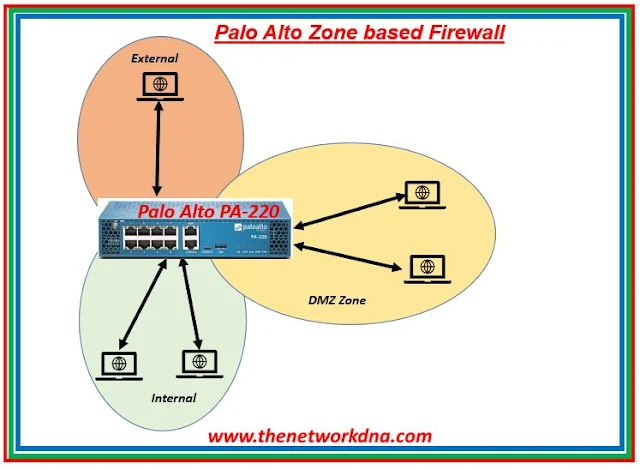 |
| Fig 1.1- Palo Alto Networks Zone Based Firewall |
Palo Alto Networks zone-based firewall
Palo Alto's zone-based firewall configuration idea is comparable to that of every other firewall. We will learn how to set up Palo Alto Zone Based Firewall.
Firewall management is set up with the use of PAN OS 8.1.0. It is advised that you review Palo Alto Networks Firewall Management Configuration if you are new to Palo Alto Firewall.
Creating Zones in Palo Alto Firewall
Step 1: Zone creating and binding to appropriate interfaces
To create the zone, we need to go to Network >> Zones and then click Add
 |
| Fig 1.2- Zones |
Step 2: Name the Zone and select zone type. Below image shows External zone, creating with L3 type. Similarly, we also created other two zones named Internal and DMZ with L3 zone type
 |
| Fig 1.3- Palo Alto Firewalls Zones |
Creating Virtual Routers in Palo Alto Firewall
Step 1: To create virtual routers, we have to go Network >> Virtual Routers and then click Add.
 |
| Fig 1.4- Palo Alto Firewalls Virtual Routers |
Step 2: Just name the Virtual Router, rest will be configured later. In our example, we are creating Virtual Routers name NDNA_VR
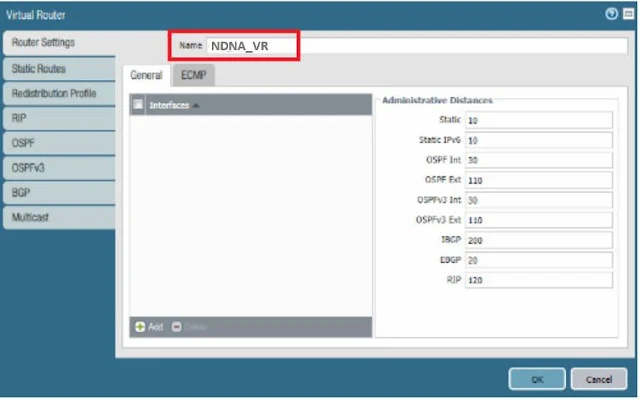 |
| Fig 1.5- Palo Alto Firewalls Virtual Routers |
Interface Configuration in Palo Alto Firewall
Step 1: For interface configuration, first of all we need to go Network >> Interfaces and then click on the interfaces.
Take Ethernet 1/3 is our outside interface. So, after clicking Ethernet 1/3, we are
giving comment (description), Interface type as Layer3. Then, we will assign the virtual router NDNA_VR and zone External.
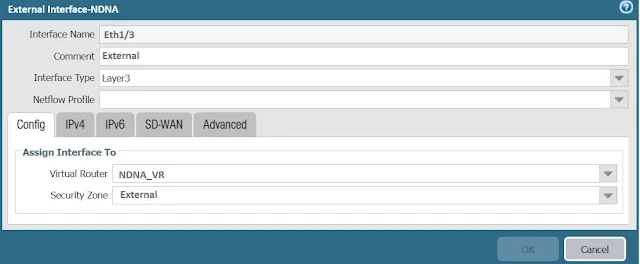 |
| Fig 1.6- Palo Alto Firewalls External Interface |
we have to add IP address. We are using IPv4, so we are clicking on IPv4 and adding the IP address for external interface by clicking Add.
 |
| Fig 1.7- Palo Alto Firewalls External Interface |
To add IP addresses for the Internal and DMZ zones, we must follow the same procedures.
Building Outside Policy
The policy must now be set up for communication from inside to outside. Interzone communication is prohibited by default.
Continue Reading...
++++++++++++++++++++++++++++++++++++++++++++++++++++
Zero Trust Network Access (ZTNA 2.0) - The Network DNA
Introduction to PaloAlto Networks Next Generations Firewall: PA7080 - The Network DNA
Introduction to Palo Alto Networks URL Filtering - The Network DNA
Palo Alto Networks: Configuring User Authentication - The Network DNA
PaloAlto Networks: Restore the configuration from backup - The Network DNA
PaloAlto Networks: Factory reset on a Palo Alto Networks device - The Network DNA
++++++++++++++++++++++++++++++++++++++++++++++++++++








