FTPS vs SFTP.. Which one is right for you ?
FTPS vs SFTP.. Which one is right for you ?
As all of you already knew that FTPS and SFTP offer strong protection through authentication options that FTP can’t provide.
 |
| Fig 1.1- SFTP Vs FTPS |
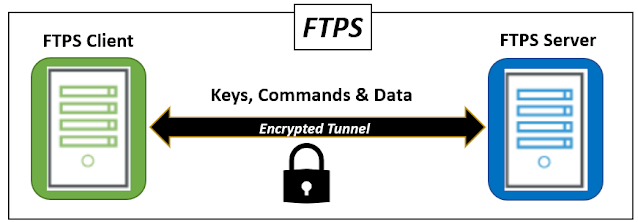
FTPS (FTP with SSL)
FTP allows you to upload, download, and delete files, create and delete directories, and read directory contents. While FTP is extremely popular, it has some drawbacks that make it difficult to utilize.
The main disadvantages are the lack of a uniform format for directory listing (this problem has been partially addressed by the introduction of the MLST command, but it is not supported by all servers) and the inclusion of a secondary connection (DATA connection). Security in FTP is achieved by using the SSL/TLS protocol for channel encryption, as defined in RFC 2228. The secured version of FTP is known as FTPS.
Pros:
- Widely known and used
- The communication can be read and understood by the human
- Provides services for server-to-server file transfer
- SSL/TLS has good authentication mechanisms (X.509 certificate features)
- FTP and SSL/TLS support is built into many internet communication frameworks.
Cons:
- Doesn’t have a uniform directory listing format
- Requires a secondary DATA channel, which makes it hard to use behind the firewalls
- Doesn’t define a standard for file name character sets (encodings)
- Not all FTP servers support SSL/TLS
- Doesn’t have a standard way to get and change file and directory attributes
SFTP (SSH File Transfer Protocol/Secure File Transfer Protocol)
SFTP (SSH File Transfer Protocol, often known as Secure FTP) is a widely used method for securely transmitting data between remote systems. SFTP was created as an extension of the Secure Shell protocol (SSH) version 2.0 to improve secure file transfer functionality.
SFTP provides file access, transfer, and management capabilities without the use of command or data channels. Instead, both data and commands are encrypted and transmitted in specially prepared binary packets via a single, secure connection via SSH.
Pros:
- Has good standards background which strictly defines most (if not all) aspects of operations
- Has only one connection (no need for DATA connection)
- The connection is always secured
- The directory listing is uniform and machine-readable
- The protocol includes operations for permission and attribute manipulation, file locking and more functionality
Cons:
- The communication is binary and can’t be logged “as is” for human reading
- SSH keys are harder to manage and validate
- The standards define certain things as optional or recommended, which leads to certain compatibility problems between different software titles from different vendors.
- No server-to-server copy and recursive directory removal operations
- No built-in SSH/SFTP support in VCL and .NET frameworks
SFTP Vs. FTPS
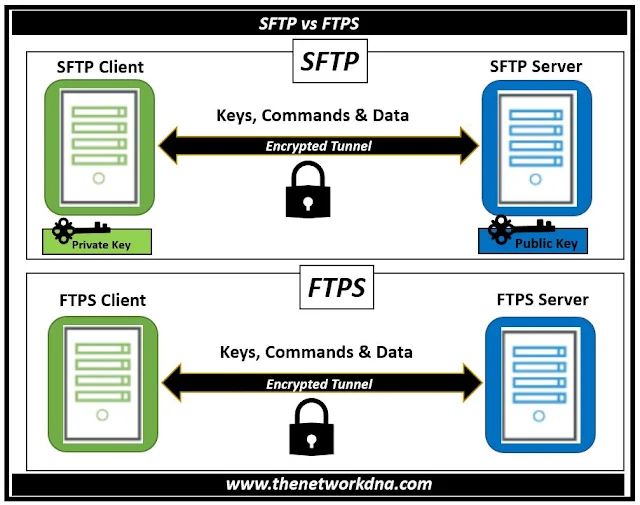
Both FTPS and SFTP use a combination of asymmetric algorithm (RSA, DSA), symmetric algorithm (DES/3DES, AES) and a key-exchange algorithm. For authentication FTPS (or, to be more precise, SSL/TLS protocol under FTP) uses X.509 certificates, while SFTP (SSH protocol) uses SSH keys. SSH key contains only a public key (the associated private key is stored separately).
Fig 1.2- SFTP vs FTPS
It doesn’t contain any information about the owner of the key. Neither it contains information that lets one reliably validate the integrity and authenticity. Some SSH software implementations use X.509 certificates for authentication, but in fact they don’t validate the whole certificate chain – only the public key is used (which makes such authentication incomplete and similar to SSH key authentication).
Continue Reading...